Git for Computer Scientists
Quick introduction to git internals for people who are not scared by words like Directed Acyclic Graph .
Source: Git for Computer Scientists, an article by Tommi Virtanen.
Quick introduction to git internals for people who are not scared by words like Directed Acyclic Graph .
Source: Git for Computer Scientists, an article by Tommi Virtanen.
The command line really wasn’t designed for secrets. So, keeping secrets secret on the command line requires some extra care and effort.
Source: How to Handle Secrets on the Command Line, an article by Carl Tashian.
This article will not turn you into an expert on Reed-Solomon. It will however allow you to understand and use any R-S codes you have to work with. In addition, you’ll learn what R-S can and can not do, and how it relates to other error correcting systems. Finally, with this understanding, the more math heavy explanations might become more accessible.
Source: Practical Reed-Solomon for Programmers, an article by Bert Hubert.
Michelle Maxwell has just wrecked her promising career at the Secret Service. Against her instincts, she let a presidential candidate out of her sight for the briefest moment and the man whose safety was her responsibility vanished into thin air.
Sean King knows how the younger agent feels. Eight years earlier, the hard-charging Secret Service agent allowed his attention to be diverted for a split second. And the candidate he was protecting was gunned down before his eyes. Now Michelle and Sean are about to see their destinies converge.
Drawn into a maze of lies, secrets, and deadly coincidences, the two discredited agents uncover a shocking truth: that the separate acts of violence that shattered their lives were really a long time in the making—and are a long way from over.
In the evening I started in Split Second, King and Maxwell Book 1 by David Baldacci. It's the first time I read a book by this author.
A while back there was a thread on one of our company mailing lists about SSH quoting, and I posted a long answer to it. Since then a few people have asked me questions that caused me to reach for it, so I thought it might be helpful if I were to anonymize the original question and post my answer here.
Source: SSH quoting, an article by Colin Watson.
I’ve been having a lot of fun using Rust for writing small tools. My day to day work involves a ton of JavaScript and Rust provides a familiar feeling, so trying out Rust was an easy decision to make. But at the same time, actually doing meaningful work in Rust requires a lot of rethinking on how to structure and reason about your code. The compiler – true to its call – is merciless; yet, for some reason, it emerges quite a pleasure in tinkering your code to make it so that it – finally! – compiles.
In this post, I am documenting – albeit in a bit funny way – some thoughts in my journey so far in Rust land, coming from the viewpoint of a hardcore JavaScript enthusiast.
Source: Rust from a JavaScript perspective.
I’ve read a lot of articles recently that seem to suggest containers kinda suck. And, well, sure. They don’t necessarily make code faster, or more secure, or much easier to debug. They require complex orchestration systems, and you can’t even use them to test your code on a different OS. Gone are the days of evangelist posts about how containers are the answer to all of life’s problems; now the think pieces have titles like, “Why You Don’t Need Docker,” and “I Did This One Weird Trick and Still Hit Kubernetes’s Scaling Limits.”
But this brand of container fatigue is largely a product of how we’re using them. I’ve often seen containers referred to as “lightweight VMs,” yet it’s this focus on containers as a form of virtualization that leads to a lot of the angst. Yes, there are parallels and points of overlap, but containers are most useful when we think of them as a tool for solving a related, but different, set of problems. They are, in fact, exceptionally helpful—as long as you’re not trying to use them to mimic an entire operating system.
Source: VMs are houses, containers are tents, an article by Nina Schiff.
In the evening I finished Phaedra: Alastor 824. While the book has a lot of references to Vance's work (and even George R. R. Martin's work) I consider the book OKish; I was expecting more.
In the morning and in the early afternoon, just before work, I wrote a
very long blog post on my experiences with creating 3 Docker images;
one for the Python version of tumblelog, one for
tweetfile, and one for the
Perl version of tumblelog. All use Alpine Linux resulting in very
small images, around 50MB each. Read all about it in A Tale of Three
Docker
Images.
In the afternoon the BBC Micro:Bit V2 GO Bundle I had ordered for Adam arrived. He has already been working with the older version of the Micro:Bit at school and was looking forward for it to arrive. I had ordered the little computer with SOS Solutions the 20th of May.

The bundle consists of a BBC Micro:Bit V2, a USB cable, a battery holder and two AAA batteries all packed in a nice small brown carton box. At first the little computer didn't work at all after I had connected the battery holder. I even tried to connect it to my Mac mini via a USB cable, but no luck. Then I decided to check out the batteries and it turned out that I had placed one the wrong way 🙃.

In the early evening Adam went to the Microsoft MakeCode for micro:bit web site and started his first project. Later he asked me if I could teach him how to program in Python 😊.
When we returned from dinner the Mini DisplayPort™ to DVI-D cable made by Cable Matters I ordered with Amazon the day before yesterday arrived.
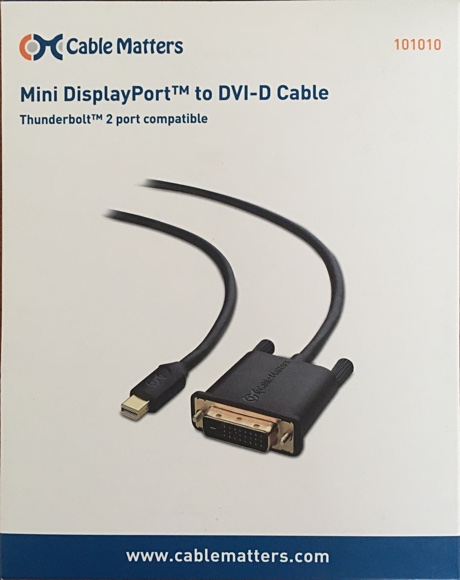
At my sister-in-law's work they had some electronics up for recycling and I managed to get a Dell E1910 monitor for free. Originally it was connected to a Raspberry Pi for the children but they rarely used the Pi so the monitor was just gathering dust. Up until today as connecting the cable was literally plug-and-play; it worked without a flaw with no configuration needed. I could now drag a window to my right and see it on a second monitor.
I am very happy with this cable. It looks good quality and both ends come with a dust cap.
In this blog post we describe how to migrate a Postgres database to a new instance with zero downtime using Bucardo. We will describe how to avoid common pitfalls like data loss, deteriorated performance and data integrity failures. We have successfully used this process to migrate our Postgres databases from version 9.5 to 12.5 on RDS, but the process isn’t restricted to RDS only, and does not depend on anything AWS specific. This migration strategy should be possible with any self-hosted or managed Postgres.
Source: Zero downtime Postgres migration, done right, an article by Rigas Papathanasopoulos.
In the morning while working on a slightly improved version of
tweetfile.pl
using inspiration from tumblelog I noticed a small bug in the
latter; I had written:
my $exit_code //= 0;
Instead of
my $exit_code = shift // 0;
in sub show_usage_and_exit. I fixed this and pushed version 5.0.1 of
tumblelog.
Later, when running the Dockerized Python version of tumblelog I got
a warning explaining that the default Loader of yaml.load() is
unsafe. In the evening I fixed this
issue and pushed 5.0.2.
HTTP content encoding is an incredibly powerful tool that can save you huge amounts of bandwidth and make your web or mobile application faster, basically for free.
Unfortunately, it's poorly understood by most developers. There's a lot of power here, but few people are aware of the options or what "content encoding" really means, so it's mostly left to be handled automatically (for better or worse) by your web server.
In many cases that means no encoding at all. In some helpful cases (typically CDNs or static site PaaS hosts) a useful basic default will be provided, but those defaults are rarely the best choice for every situation.
With just a tiny sprinkle of knowledge, you can enable this and speed up your web application, your API, and all your HTTP requests & responses in no time at all.
Source: Encoding your HTTP for fun and profit, an article by Tim Perry.
There weren’t as many web fonts to pick from when I started my freelance career in the early 2000s, still I was always overwhelmed by the number of fonts to choose from. With no formal education in design or typography, my choices were uninformed and limited.
It’s kinda funny to look back and realise that it was harder for me to choose fonts when there were fewer to choose from than now. I had moved away from being a freelance graphic designer in the years since then, but I still do branding, web design and graphic design work for my own projects. I acquired enough experience and learned so much about web typography in my career that I naturally came to the conclusion that many designers had reached before me—all you need is 5 fonts.
Source: All you need is 5 fonts, an article by Matej Latin.
Even in the age of smartphones I still prefer to check the calendar on my computer and I’ve often been disappointed by the horrible default calendars that ship with some operating systems (e.g. macOS’s calendar accessible via its systray).
Fortunately for us, Emacs users, we always have access to a proper calendar regardless of our OS and desktop environment (if any) -
M-x calendar.
Source: Emacs as Your Calendar, an article by Bozhidar Batsov.
Maybe it's just me, but I hate stupid examples. I hate reading about OOP with animal examples as much as I hate reading about async with the client using bare
asyncio.sleepstatements. Mostly because (considering you won't work for a zoo 🤷) these examples will never get any close to real life.I want then to explore async without talking about food (although I'm hungry right now) and using examples that you can run yourself and understand. So, the plan is to:
- Explore
asyncwith slow HTTP queries;- Explore
asyncwith slow Database queries;- Share a real project running in production that uses
async;
Source: Async python in real life 🐍🔀, an article by Guilherme Latrova.
In the evening I debugged a Docker container. I want to "Dockerize" several scripts which I now run in an outdated Ubuntu virtual machine on my Mac mini so I can run them in Docker Desktop. Still a virtual machine on MacOS but I can now call them from the MacOS command line.
We use Docker Official Images as the base images for several of our services. It's a popular choice, and there are good reasons for this. A dedicated team reviews them at Docker and gets actively maintained by experts from their respective communities, including the security community.
When we first started building these images, we struggled to integrate the process used to release fixes to the community. I can summarize our problems into two high-level buckets:
- We were missing security and bug fixes. By missing, I mean that we weren't applying them quickly, or we weren't applying them at all.
- Our builds were breaking mysteriously. Maybe all build breakages are mysterious, but this class of breakages was really bizarre!
It wasn't that patches weren't flowing in. The maintainers were doing a great job. It turned out that we needed a better approach for managing our Dockerfiles. We needed a Docker policy that could take advantage of the security and bug fixes that were reliably streaming in. And that was something we were missing entirely.
Source: Maintaining Docker Official Images an article by Jim Clark.
CSS offers a number of different units for expressing length. Some have their history in typography, such as point (pt) and pica (pc), others are known from everyday use, such as centimeter (cm) and inch (in). And there is also a “magic” unit that was invented specifically for CSS: the px. Does that mean different properties need different units?
No, the units have nothing to do with the properties, but everything with the output media: screen or paper.
Source: CSS: em, px, pt, cm, in…, an article by Bert Bos.
Anybody who has the responsibility of maintaining a cluster of systems knows about the vulnerability remediation lifecycle: vulnerabilities are discovered, disclosed to vendors, mitigated by vendors and then consumers deploy the mitigations as they update their systems.
In the proprietary software world, the deployment phase is colloquially known as Patch Tuesday, because many vendors release patches on the second and fourth Tuesday of each month. But how does all of this actually happen, and how do you know what patches you actually need?
I thought it might be nice to look at all the moving pieces that exist in Alpine’s remediation lifecycle, beginning from discovery of the vulnerability, to disclosure to Alpine, to user remediation. For this example, we will track CVE-2016-20011, which I just fixed in Alpine, which is a minor vulnerability in the
libgrsslibrary concerning a lack of TLS certificate validation when fetchinghttpsURIs.
Source: the vulnerability remediation lifecycle of Alpine containers, an article by Ariadne Conill.
In the early afternoon I pushed tumblelog 5.0.0 to
GitHub. This major update
adds support for tagging posts. If you follow my blog you probably
have already seen one or more tags underneath each posts, and maybe
even the tag cloud.
If you run your own tumblelog please read the
CHANGELOG.md
and the
README.md. Together
they are hopefully enough to get you started with 5.0.0. If you
encounter any issues or have any questions please let me
know.
This tutorial is an in-depth look at how Git works, performing a lot of sometimes unusual steps to walk through interesting details. You will have to pay attention closely, or you will get lost on the way. But do not despair; you can run this tutorial on your computer, at the speed you want, skip to any step you want, and investigate the state of things in another terminal window at all times.
Source: A Random Walk Through Git.
q is a command line tool that allows direct execution of SQL-like queries on CSVs/TSVs (and any other tabular text files).
q treats ordinary files as database tables, and supports all SQL constructs, such as WHERE, GROUP BY, JOINs etc. It supports automatic column name and column type detection, and provides full support for multiple encodings.
Source: q - Text as Data, an article by Harel Ben-Attia.
A side effect of the whole freenode kerfluffle is that I’ve been looking at IRCD again. IRC, is of course a very weird and interesting place, and the smaller community of people who run IRCDs are largely weirder and even more interesting.
However, in that community of IRCD administrators there happens to be a few incorrect systems programming opinions that have been cargo culted around for years. This particular blog is about one of these bikesheds, namely the kqueue vs epoll debate.
You’ve probably heard it before. It goes something like this, “BSD is better for networking, because it has kqueue. Linux has nothing like kqueue, epoll doesn’t come close.” While I agree that epoll doesn’t come close, I think that’s actually a feature that has lead to a much more flexible and composable design.
Source: actually, BSD kqueue is a mountain of technical debt, an article by Ariadne Conill.